What are the limitations of intrusion detection system?
Limitations. Noise can severely limit an intrusion detection system’s effectiveness. Bad packets generated from software bugs, corrupt DNS data, and local packets that escaped can create a significantly high false-alarm rate. It is not uncommon for the number of real attacks to be far below the number of false-alarms.
Which one is the disadvantages of network based IDS?
The drawback to a network-based IDS is its cost. A network-based IDS relies on additional hardware in the form of network probes. Additional drawbacks to network-based IDS are the following: IDS manipulation with fragmentation and TTL exploits.
What is a disadvantage of using an IPS compared to an IDS?
An IDS leaves a window for an attacker to cause damage to a target system, while a false positive detection by an IPS can negatively impact system usability.
Which are known weakness of automated intrusion detection systems?
They Do Not Process Encrypted Packets An IDS cannot see into encrypted packets, so intruders can use them to slip into the network. An IDS will not register these intrusions until they are deeper into the network, which leaves your systems vulnerable until the intrusion is discovered.
What are one advantage and one disadvantage to placing a sensor directly behind the network border firewall?
Placing a sensor’s monitoring interface behind a filtering router or firewall prevents the sensor from monitoring traffic the filtering router rejects. One disadvantage to this placement strategy is the sensor is unaware of any policy violations the filtering device stops.
What are the differences between the intrusion detection system IDS and intrusion prevention system IPS in network security?
IPS: What is the Difference? Intrusion Detection Systems (IDS) analyze network traffic for signatures that match known cyberattacks. Intrusion Prevention Systems (IPS) also analyzes packets, but can also stop the packet from being delivered based on what kind of attacks it detects — helping stop the attack.
How does intrusion affect security?
An intrusion, then, is any action taken by an adversary that has a negative impact on the confidentiality, integrity, or availability of that information. Having physical access to a computer system allows an adversary to bypass most security protections put in place to prevent unauthorized access.
What is the difference between an intrusion detection system and an intrusion protection system?
Intrusion Detection Systems (IDS) analyze network traffic for signatures that match known cyberattacks. Intrusion Prevention Systems (IPS) also analyzes packets, but can also stop the packet from being delivered based on what kind of attacks it detects — helping stop the attack.
What are the advantages of intrusion detection system?
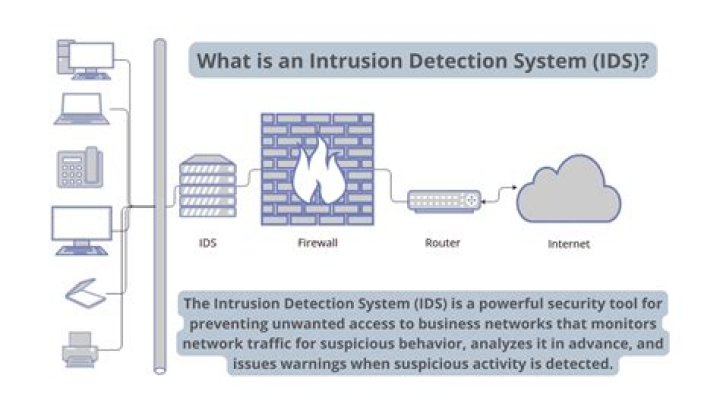
The primary benefit of an intrusion detection system is to ensure IT personnel is notified when an attack or network intrusion might be taking place. A network intrusion detection system (NIDS) monitors both inbound and outbound traffic on the network, as well as data traversing between systems within the network.
How does an intrusion prevention system differ from an intrusion detection system quizlet?
Intrusion Detection System – A device or application that analyzes whole packets, both header and payload, looking for known events. Intrusion Prevention System – A device or application that analyzes whole packets, both header and payload, looking for known events.
How does an IPS differ from an idea?
The primary difference between the two is that one monitors while the other controls. IDS systems don’t actually change the packets. They just scan the packets and check them against a database of known threats. IPS systems, however, prevent the delivery of the packet into the network.
How can network breaches be prevented?
Below, we discuss six solidly proven ways to prevent cyber security breaches from occurring at your company.
- Limit access to your most valuable data.
- Third-party vendors must comply.
- Conduct employee security awareness training.
- Update software regularly.
- Develop a cyber breach response plan.