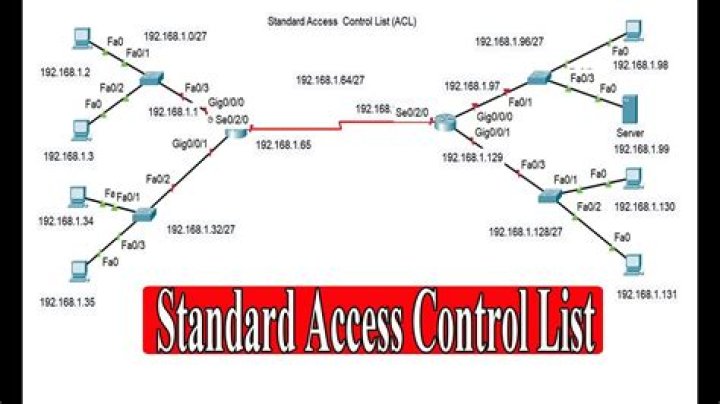
What are access control lists Cisco?
The Cisco Access Control List (ACL) is are used for filtering traffic based on a given filtering criteria on a router or switch interface. Based on the conditions supplied by the ACL, a packet is allowed or blocked from further movement.
What is Access Control List?
An access control list (ACL) contains rules that grant or deny access to certain digital environments. There are two types of ACLs: Filesystem ACLs━filter access to files and/or directories. Filesystem ACLs tell operating systems which users can access the system, and what privileges the users are allowed.
How do Cisco access lists work?
An ACL is a list of permit or deny rules detailing what can or can’t enter or leave the interface of a router. Every packet that attempts to enter or leave a router must be tested against each rule in the ACL until a match is found. If no match is found, then it will be denied.
How do I find the access list on my Cisco router?
Use the show interfaces command to see a list of all interfaces currently configured on the router.
What are the benefits of access control list?
The advantages of using access control lists include:
- Better protection of internet-facing servers.
- More control of access through entry points.
- More control of access to and traffic between internal networks.
- More granular control of user and group permissions.
What are the two types of IP access list?
There are two main different types of Access-list namely:
- Standard Access-list – These are the Access-list that are made using the source IP address only. These ACLs permit or deny the entire protocol suite.
- Extended Access-list – These are the ACL that uses source IP, Destination IP, source port, and Destination port.
Where is the access control list?
Access control lists (ACLs) can control the traffic entering a network. Normally ACLs reside in a firewall router or in a router connecting two internal networks.
How do I create an access control list?
Procedure
- If the connection you want to create the ACL for is not open, search for and select the connection.
- Select Add a new list from the Access Control List (ACL) drop-down list.
- Enter a name and description.
- Enter the remaining ACL settings. Setting. Description. Access for Users.
- Click Save New ACL.
How do you implement access control list?
Configuring Access Control Lists
- Create a MAC ACL by specifying a name.
- Create an IP ACL by specifying a number.
- Add new rules to the ACL.
- Configure the match criteria for the rules.
- Apply the ACL to one or more interfaces.
How do I view access control lists?
To view a policy access control list, click a domain’s name from the Domains pane in the Policy Administration window and select the Access Control Rules tab. In the Search Results table, click the view access control lists icon . The View Access Control Lists window opens.
What are main tasks of the access control lists?
Access control lists are permission-based systems that assign people in an organization different levels of access to files and information. They function as permission slips indicating that a user needs to open a particular network device, file, or other information.