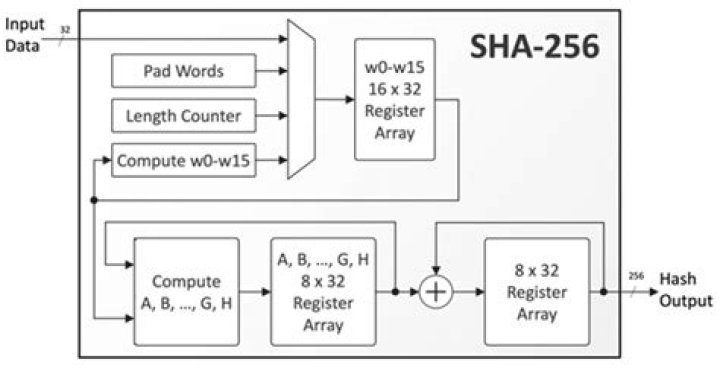
Is Sha-256 still used?
Is Sha-256 still used?
SHA-256 is used in some of the most popular authentication and encryption protocols, including SSL, TLS, IPsec, SSH, and PGP. In Unix and Linux, SHA-256 is used for secure password hashing. Cryptocurrencies such as Bitcoin use SHA-256 for verifying transactions.
Can Sha-256 be broken?
The SHA-256 algorithm is not yet easily cracked. Moreover SHA256 algorithm, such as SHA-512 algorithms compared to other secure top model is calculated more quickly is currently one of the most widely used algorithms. However, IT experts talk about allegations and developments that SHA-256 may be vulnerable very soon.
Is Sha-256 and AES 256 same?
AES (all of its forms) is a block cipher, while SHA-256 is a hash function.
Who invented SHA256 algorithm?
National Security Agency
SHA-256, or Secure Hash Algorithm 256, is a hashing algorithm used to convert text of any length into a fixed-size string of 256 bits (32 bytes). Originally published in 2001, SHA-256 was developed by the US Government’s National Security Agency (NSA).
Why is SHA-256 irreversible?
SHA256 is a hashing function, not an encryption function. Secondly, since SHA256 is not an encryption function, it cannot be decrypted. What you mean is probably reversing it. In that case, SHA256 cannot be reversed because it’s a one-way function.
Who invented SHA256?
The SHA-2 family consists of six hash functions with digests (hash values) that are 224, 256, 384 or 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, SHA-512/256….SHA-2.
| General | |
|---|---|
| Designers | National Security Agency |
| First published | 2001 |
| Series | (SHA-0), SHA-1, SHA-2, SHA-3 |
| Certification | FIPS PUB 180-4, CRYPTREC, NESSIE |
Does SHA256 need a key?
Does SHA256 need a key? – Quora. No, it doesn’t. SHA-256 just creates a unique, irreversible and cryptographically secure hash over a message, the sole input parameter to the hash function.
Can AES be used for hashing?
AES-hash is a secure hash mode for AES, with the same properties and key length as SHA-256. Its advantage is greater performance. Rijndael is used in 256-bit key, 256-bit block mode. First, the file to be hashed is padded to make it’s length be an even multiple of the block size and include a length encoding.
Is Sha 2 symmetric or asymmetric?
Hashing vs Encryption
| Encryption | Hashing |
|---|---|
| There are two primary types of encryption: Symmetric key encryption (or private key encryption) andAsymmetric key encryption (or public key encryption) Examples of encryption algorithms: RSA, AES, DES, etc. | Examples of hashing algorithms: SHA-1, SHA-2, MD5, Tiger, etc. |
Does Bitcoin use SHA-256?
Bitcoin uses double SHA-256, meaning that it applies the hash functions twice. The algorithm is a variant of the SHA-2 (Secure Hash Algorithm 2), developed by the National Security Agency (NSA).
Can you brute force SHA256?
Cracking a SHA-256 Hash But hashes can be reversed using methods such as dictionary attacks which compares the given hash to the hashes of common words from a dictionary or brute-force which computes the hash of many different combinations of characters until it finds one that matches the given hash.
Can you reverse hashes?
Hash functions are not reversible in general. MD5 is a 128-bit hash, and so it maps any string, no matter how long, into 128 bits. Obviously if you run all strings of length, say, 129 bits, some of them have to hash to the same value.